Using ThreatEye
Logging into ThreatEye
ThreatEye uses Role Based Access Control (RBAC) to restrict access to various components of ThreatEye. Your ThreatEye admin assigns the roles for various users. If you are assigned an Administrator role, you have full access to all ThreatEye components, including the Settings options. If you are not assigned an Administrator role, the Settings options are not displayed and available when you log into ThreatEye.
To log into ThreatEye:
1. Enter the URL provided by LiveAction into your browser to access the ThreatEye login screen.
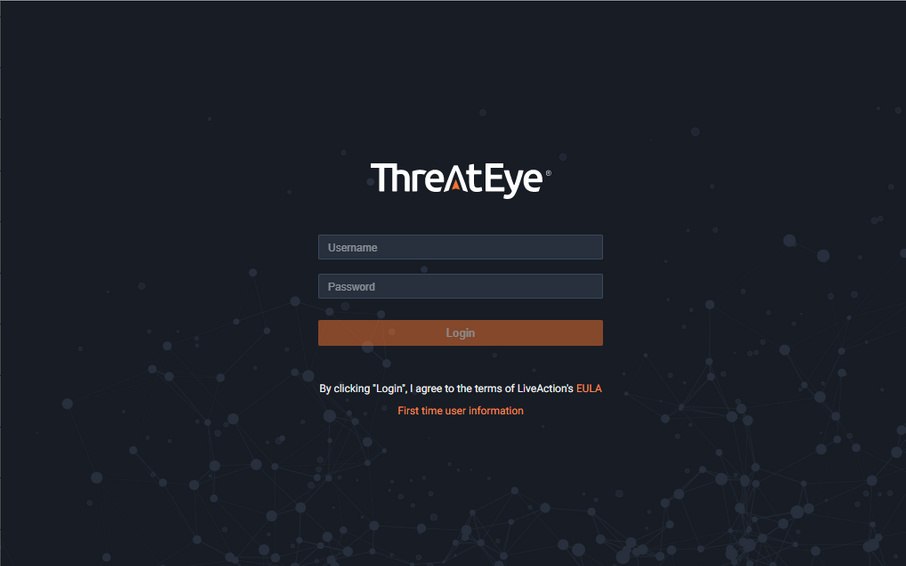
2. Enter your Username and Password and click .
NOTE: Your access to ThreatEye is available for one hour. After one hour, you will automatically be logged out of ThreatEye and you will need to log in again if you want to continue using ThreatEye.